When it comes to innovation, project teams encounter a host of unique challenges and unknowns. In these scenarios, a systems engineer's unique skills are vital to bring pioneering technologies to life.
The Value of Systems Engineering in Medical Device Development
Medical device development is all about making the right product as efficiently as possible. Learn how applying good systems engineering practices can make projects up to three times more likely to be successful.

New Perspectives on Accelerating Genetic Nanomedicines Through the Regulatory Pathway
Explore how we can accelerate genetic nanomedicines through regulatory pathways and pave the way for powerful, personalized treatments.

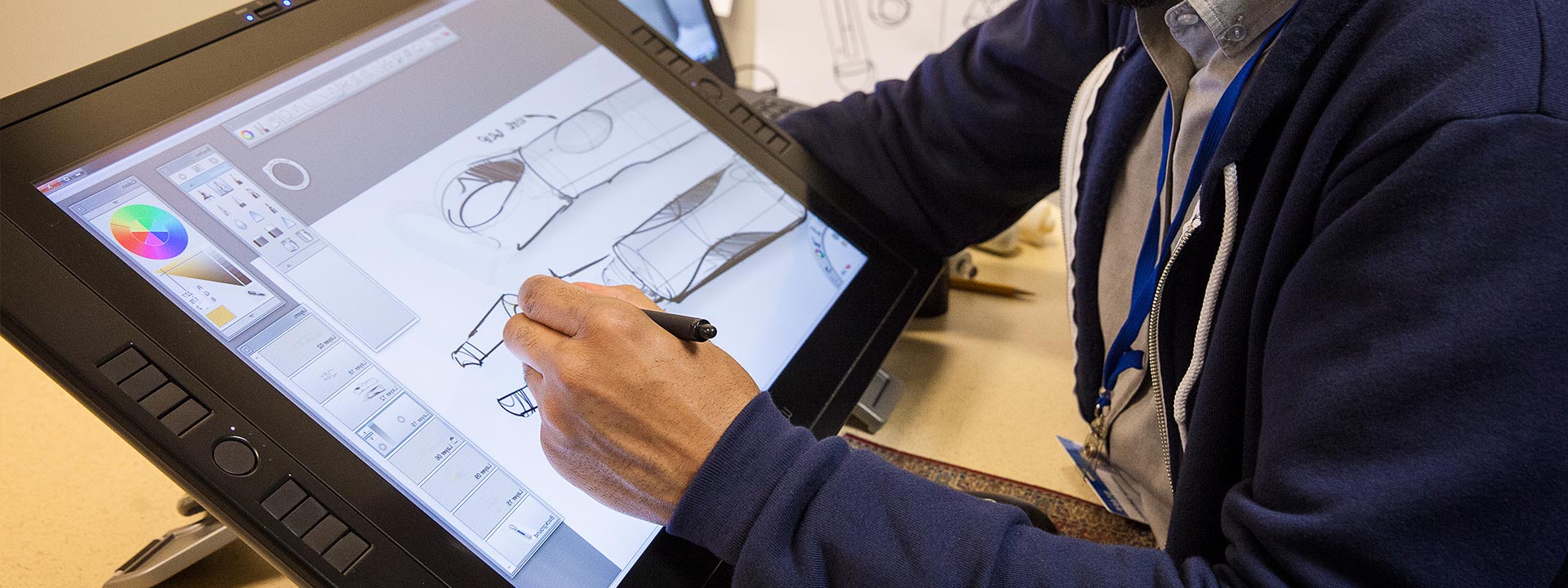
Contract Design and Development vs. In-House: How to Find the Best Fit for Your Organization
Medical device design and development can be technically complex. The right resources and expertise can help you navigate the regulatory environment and manage risk.

Deploying a Circular Economy for Medical Devices
Sustainability and ESG initiatives have taken center stage, often leaving organizations uncertain. Learn how how medical device companies can deploy a circular economy based on sustainable practices.

10 Ways to Align Your Medical Device with Human Factors Industry Best Practices
Integrating the user early and often into the process enables devices to be built for user behaviors. Here's 10 ways to align your medical device with Human Factors Industry Best Practices.
Sign Up for Battelle Updates
Follow along with the latest news, announcement and updates from our Battelle community of solvers.